Cuibit publishes insights from shipped delivery work across web, WordPress, AI and mobile. Articles are written for real buying and implementation decisions, then updated as the stack or the advice changes.
Cuibit Web Engineering
Web architecture and technical SEO team
The Cuibit team covering web architecture, Next.js delivery, technical SEO and buyer-facing product surfaces.
React and Next.js Security Hardening: What SaaS Teams Should Patch Now in 2026

Key takeaways
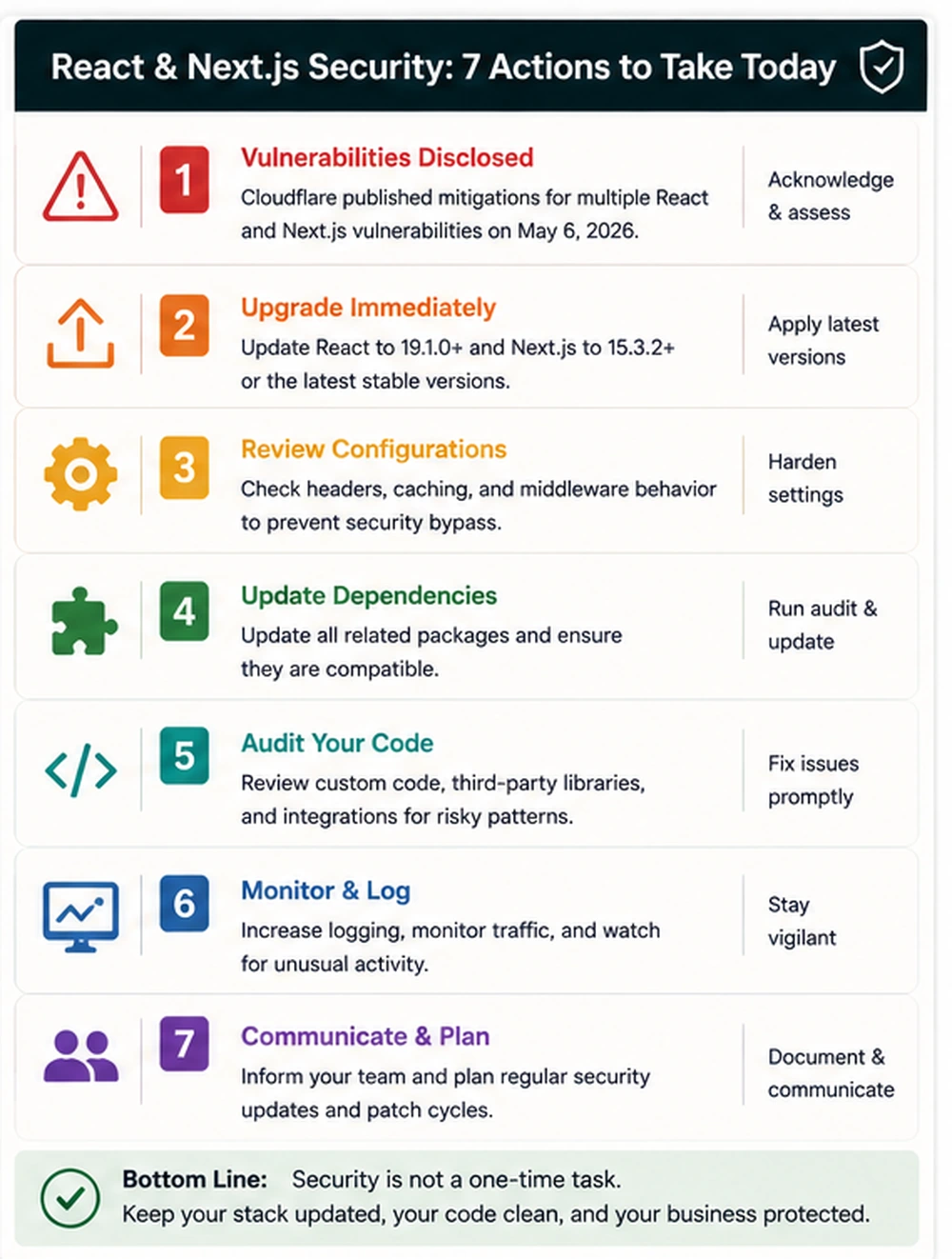
- Recent React and Next.js vulnerability disclosures make security hardening a live business issue for SaaS platforms, dashboards, ecommerce front ends, and custom web applications using React Server Components or the Next.js App Router.
- The practical response is not only "run npm update." Teams need dependency inventory, affected route review, middleware checks, edge protection, CI testing, cache review, observability, and a safe release plan.
- Apps using React Server Components, Next.js App Router, self-hosted Node servers, rewrites, middleware, proxy behavior, caching, or custom request handling deserve immediate review.
- Patched dependency versions matter, but version upgrades should be paired with QA. Security fixes can affect routing, rendering, caching, headers, server actions, middleware behavior, and deployment adapters.
- For business websites and SaaS products, security patching is part of product reliability. A broken patch, a missed vulnerability, or a rushed deployment can all damage trust.
- The safest operating model is a recurring patch-readiness process: know your stack, subscribe to advisories, update quickly, test critical journeys, monitor logs, and document what changed.
Why this topic matters now
React and Next.js are at the center of modern web development. They power marketing sites, SaaS products, admin dashboards, marketplaces, internal tools, ecommerce storefronts, and customer portals. That popularity makes them valuable, but it also means security advisories matter quickly. When vulnerabilities affect React Server Components or Next.js routing behavior, the business impact can extend beyond engineering teams.
The latest React and Next.js advisories are a reminder that full-stack JavaScript applications are not just front-end code. A modern Next.js app may handle server rendering, server actions, middleware, proxy behavior, API routes, cache control, authentication boundaries, edge deployments, image optimization, and backend integrations. A vulnerability in that stack can affect availability, data access, request routing, or user trust.
For Cuibit clients, this topic connects directly to React development, Next.js development, SaaS engineering, backend reliability, and technical maintenance. Businesses often think of React and Next.js as speed and user-experience choices. They are also operational choices. The more business-critical the application, the more disciplined the patch process needs to be.
This guide explains what SaaS teams, ecommerce teams, and product owners should do now: identify exposure, patch safely, test the right surfaces, harden deployment, and turn the current vulnerability cycle into a stronger long-term process.
What happened: the short business version
Multiple vulnerabilities have recently been disclosed across React Server Components and Next.js. Cloudflare summarized the affected surface as including denial of service, middleware and proxy bypass, server-side request forgery, cross-site scripting, and cache poisoning issues across a range of severity levels. Cloudflare also recommended updating React-related packages and Next.js immediately, with patched versions available for React Server Components packages and Next.js releases.
The technical details matter to developers, but business leaders should focus on the operating risk:
- Some vulnerabilities can affect availability.
- Some can affect trust boundaries between routes or middleware.
- Some can affect how requests are proxied.
- Some can affect cache behavior.
- Some can affect self-hosted deployments differently than managed deployments.
- Some require both dependency patching and configuration review.
That means teams should avoid two bad responses. The first bad response is panic: rushing patches to production without testing. The second bad response is delay: assuming a managed host, WAF, or framework update removes all risk without confirming the application's actual setup.
A mature team does both: update quickly and test carefully.
Why React and Next.js vulnerabilities are different from normal front-end bugs
Traditional front-end bugs often affect the browser experience. They can break a layout, cause a button not to work, or create a client-side error. Modern Next.js bugs can be different because Next.js often sits across the boundary between browser, server, middleware, edge, and backend services.
A Next.js application may include:
- server-rendered pages
- React Server Components
- API routes
- middleware
- rewrites and redirects
- server actions
- authentication checks
- cache layers
- image optimization
- streaming responses
- edge functions
- Node server behavior
- third-party APIs
- custom headers
- environment variables
This makes security review more complex. A route that looks like a page may rely on server logic. A middleware rule may act as an authentication gate. A rewrite may forward traffic to a backend. A cache setting may decide whether personalized content is stored or reused. A server action may accept data that changes state.
Security hardening has to inspect the full request lifecycle, not only the component tree.
Who should pay attention first
Not every site has the same risk profile. Prioritize review if your application uses any of these patterns.
You use the Next.js App Router
The App Router is common in modern Next.js builds and is closely tied to React Server Components. If your app uses the App Router, review versions, server component packages, route behavior, and framework advisories carefully.
You self-host Next.js
Self-hosted apps may have different exposure than apps deployed to managed platforms that handle routing, edge protection, or rewrites differently. Self-hosted Node servers should be reviewed for request handling, proxy behavior, headers, and infrastructure-level mitigations.
You use middleware for authentication or routing
Middleware is often used for redirects, authentication checks, locale routing, A/B tests, and access control. Any advisory involving middleware or bypass behavior deserves immediate testing.
You use rewrites or proxies
Rewrites and proxies can be convenient, but they can also create hidden request paths. Review where traffic can be forwarded, which methods are allowed, and whether backend routes have their own authentication.
You handle sensitive data
Dashboards, healthcare portals, finance tools, B2B SaaS products, admin panels, and ecommerce account areas should patch quickly and test thoroughly.
You have high traffic
Denial-of-service vulnerabilities become more serious for high-traffic applications. Availability is a business risk, not only an infrastructure issue.
A practical patch plan for engineering teams
The safest response is a structured patch plan. The goal is speed with control.
Step 1: Inventory the application
Start by identifying where React and Next.js are used. Many companies have more than one application: marketing site, app dashboard, admin tool, documentation site, checkout front end, and internal portal.
Document the Next.js version, React version, React Server Components packages, hosting platform, middleware usage, App Router or Pages Router usage, rewrites, API routes, server actions, authentication system, cache layer, WAF or edge protection, CI test coverage, and deployment process.
This step prevents teams from patching the obvious app while missing a smaller internal tool or admin route.
Step 2: Check official advisories and patched versions
Use official framework, hosting, and security advisories as the source of truth. Third-party summaries are useful for awareness, but the final upgrade target should come from official sources.
For the current cycle, Cloudflare's advisory points teams toward patched versions for React Server Components packages and Next.js. If your stack uses additional framework adapters, hosting integrations, or custom runtime behavior, check those release notes too.
Step 3: Patch in a branch
Do not update production directly. Create a security patch branch, update dependencies, commit lockfile changes, and note exactly what changed.
For teams with multiple applications, use consistent branch naming and release notes. Security patches should be easy to audit later.
Step 4: Run automated checks
Run the full test suite: unit tests, integration tests, end-to-end tests, linting, type checks, build process, dependency audit, security scanners, route tests, and performance smoke tests.
If the app lacks test coverage, prioritize manual testing of the most important user journeys before release.
Step 5: Test the request lifecycle
Because many vulnerabilities involve server behavior, test more than visual pages. Review protected routes, unauthenticated routes, middleware paths, API endpoints, rewrites, redirects, server actions, cache behavior, error handling, custom headers, content security policy, login, logout, role-based access, admin routes, checkout flows, and webhook endpoints.
This is where experienced frontend development and backend review need to work together. The issue may surface in a route, but the risk can involve authentication, caching, and server behavior.
Step 6: Add edge mitigations where appropriate
If your provider or WAF offers mitigation rules, review them. Edge rules can reduce immediate exposure while patches are tested, especially for denial-of-service or suspicious request patterns.
However, WAF rules should not be treated as a replacement for patching. They are an additional layer.
Step 7: Deploy with monitoring
Schedule deployment when the team can monitor. Watch logs, errors, traffic patterns, response times, authentication errors, failed API calls, checkout issues, and customer reports.
Security patching should have a post-deploy checklist, not just a merge button.
Step 8: Document the response
Record what versions were affected, which apps were patched, which tests were run, which mitigations were added, who reviewed the release, and whether follow-up work is needed. This documentation helps with audits, client communication, and future incident response.
What business owners should ask their development team
If you are a founder, product owner, CTO, or operations leader, you do not need to inspect every dependency yourself. But you should ask clear questions.
- Do we use React, Next.js, or React Server Components anywhere?
- Which applications are affected?
- Are we using Next.js App Router?
- Are any apps self-hosted?
- Are we using middleware for authentication or redirects?
- Do we have rewrites or proxy behavior?
- Have we updated to patched versions?
- Did we test login, checkout, admin, API, and key user flows?
- Do we have WAF or edge mitigation enabled?
- What monitoring is in place after deployment?
- What is the rollback plan?
- What is our recurring dependency patch process?
A confident team should be able to answer without guessing.
Hardening beyond the patch
Patching is urgent, but it should not be the end of the work. A vulnerability cycle is a chance to improve the system.
Improve dependency visibility
Use dependency dashboards, lockfile review, automated alerts, and ownership labels. Every application should have someone responsible for updates.
Add route-level tests
Critical routes need tests. Login, checkout, account access, admin dashboards, API endpoints, and protected pages should not rely only on manual QA.
Review middleware design
Middleware should be simple, explicit, and tested. Avoid hiding too much business logic in middleware without route-level safeguards.
Strengthen backend authorization
Do not rely only on front-end visibility or middleware assumptions. Backend routes should enforce their own authorization. This is especially important for dashboards, account areas, and API endpoints.
Cuibit's backend development work often focuses on exactly this kind of boundary: making sure business rules and data access are enforced where they actually matter.
Review cache behavior
Cache poisoning and personalized content leaks can be serious. Review which routes are cached, which headers control caching, and whether user-specific data can be cached accidentally.
Add security review to release planning
A release plan should include dependency checks, route checks, and security-sensitive file review. This does not need to slow every release, but it should be part of the process for framework upgrades.
Special concerns for SaaS products
SaaS products often have authenticated dashboards, role-based access, tenant boundaries, billing, integrations, and admin controls. That makes React and Next.js security more important.
For SaaS teams, patch testing should include tenant isolation, user roles, team permissions, billing pages, admin pages, API tokens, integrations, invite flows, password reset, webhook handling, audit logs, data export, account deletion, and support impersonation if used.
The key risk is not only whether the app runs. It is whether users can access only what they should access. A patched app that breaks permissions can still create serious business problems.
For teams building SaaS dashboards or internal platforms, a security patch cycle should be combined with architecture review. Cuibit's custom React enterprise dashboard example is relevant because dashboards often combine complex UI, sensitive data, and role-based workflows.
Special concerns for ecommerce
Ecommerce applications using React or Next.js may be headless storefronts, Shopify front ends, WooCommerce front ends, product configurators, marketplaces, or custom checkout flows.
Patch testing should include product listing pages, product detail pages, cart, checkout, payment redirect, shipping calculation, coupons, account login, order history, product search, inventory display, analytics events, tracking pixels, structured data, redirects from old URLs, and cache behavior for prices and stock.
Ecommerce risk is visible quickly. A broken cart or login flow affects revenue. A cache issue can show stale prices. A rewrite issue can break backend calls. A middleware issue can affect customer accounts.
For headless commerce, coordination between frontend, backend, and ecommerce platform is essential. If the storefront is patched but the API assumptions change, the customer experience can still break.
Special concerns for marketing and content sites
Marketing sites may seem lower risk, but many are built with Next.js and connect to CMS systems, lead forms, analytics, personalization, and conversion tracking.
Test landing pages, contact forms, lead capture, CMS previews, redirects, sitemap generation, schema output, analytics, A/B testing, gated content, localization, and performance.
A broken lead form after a framework patch can quietly waste ad spend. A broken canonical or redirect can affect SEO. A patch should include business-facing checks, not only developer checks.
The role of hosting and infrastructure
Hosting changes the risk model. Managed platforms may provide framework-specific mitigations, but they do not remove the need to update dependencies. Self-hosted environments require more internal responsibility.
Review Node runtime version, reverse proxy behavior, WAF rules, CDN cache rules, edge functions, request size limits, method restrictions, logging, rate limiting, health checks, secret management, and deployment rollback.
For self-hosted Next.js, infrastructure review is especially important because the app may be responsible for behavior that a managed platform would handle elsewhere.
A 48-hour response plan
If your team has not reviewed the latest advisories yet, use this short response plan.
First 6 hours
Create an inventory. Identify React and Next.js apps. Check versions. Find App Router usage, middleware, rewrites, and self-hosted deployments. Add temporary WAF or edge rules if available.
First 24 hours
Patch dependencies in staging. Run automated tests. Manually test critical flows. Review logs. Confirm authentication, checkout, admin, and API behavior.
First 48 hours
Deploy patched versions with monitoring. Document the response. Add follow-up tasks for weak tests, unclear ownership, dependency alerting, and route hardening.
For many teams, this process will reveal wider maintenance issues. That is normal. Use the urgency to build a better system.
When to bring in outside help
Bring in outside help if the application is revenue-critical, the team is unsure which apps are affected, the app uses custom middleware or proxy logic, the app is self-hosted, the app has weak test coverage, the application has sensitive customer data, or the team cannot safely patch without breaking production.
This is not only emergency work. A strong partner can help turn patching into a better maintenance model.
Cuibit's custom web development and Next.js development teams can support dependency upgrades, architecture review, frontend testing, backend boundary checks, and release planning for business-critical web applications.
What a mature patch process looks like
A mature team does not wait for a crisis. It has a repeatable process.
A good process includes dependency ownership, automated alerts, weekly patch review, emergency patch path, staging environment, test coverage for key journeys, WAF or edge rule review, rollback plan, release notes, post-deploy monitoring, security review for middleware and backend routes, and documented incident response.
This process is not bureaucracy. It is how teams move quickly without guessing.
For applications that already suffer from reliability problems, security patching may expose deeper architectural issues. In that case, a focused reliability project may be more useful than repeatedly patching symptoms. Cuibit's backend reliability rebuild work is relevant because security, uptime, and maintainability often depend on the same engineering foundations.
How this fits into a broader web development strategy
React and Next.js are excellent tools when used with discipline. They support fast interfaces, flexible rendering, reusable components, and strong developer experience. But modern web applications need more than speed. They need maintainable architecture, security review, observability, accessibility, SEO support, and release discipline.
A business choosing a framework should ask whether the team can maintain it, patch it quickly, understand the hosting model, monitor production, roll back safely, and keep routes and permissions clear.
The right technology stack is the one the business can operate safely.
Editorial conclusion
React and Next.js security hardening is not just a developer task. It is a business continuity task. The same framework features that make modern web applications powerful also make patching more important: server rendering, middleware, server components, caching, routing, and backend integrations all sit close to revenue and user trust.
The immediate action is clear: identify affected apps, update to patched versions, test critical flows, add edge mitigations where useful, and deploy with monitoring. The deeper lesson is just as important: every serious web application needs a patch process before the next advisory arrives.
For SaaS teams, ecommerce brands, and companies running custom dashboards, this is the moment to treat frontend security as part of product operations. Patch now, document what changed, and use the work to build a stronger, safer release system.
Need this advice turned into a real delivery plan?
We can review your current stack, pressure-test the tradeoffs in this guide and turn it into a scoped implementation plan for your team.